Published On Jun 10, 2022
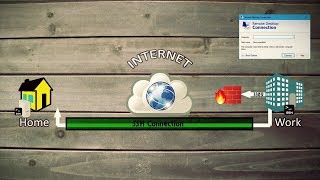
** To manage Windows Servers using winrm: • Learn How to Use Ansible to Manage Wi... ""
* Issue - During the OpenSSH install, the original command was failing. I've added the updated command below so it the command fails, try the new command. - **
For this demo, we’re going to complete the following steps:
• Install SSH
• Configure Ansible to connect on port 22 to our Windows 2022 server
• Test the Ansible CLI works
• Create a playbook and test that work.
Chapters:
Build a Windows 2022 server in AWS: • Use Ansible to Manage Windows Servers...
Add port 22/SSH to the security group: • Use Ansible to Manage Windows Servers...
RDP onto the remote Windows 2022 server: • Use Ansible to Manage Windows Servers...
Install OpenSSH on our Windows 2022 server: • Use Ansible to Manage Windows Servers...
SSH onto the Windows 2022 server from Linux: • Use Ansible to Manage Windows Servers...
Setup Ansible to connect to our Windows 2022 server: • Use Ansible to Manage Windows Servers...
Check Ansible connectivity using win_ping: • Use Ansible to Manage Windows Servers...
Setup a playbook to run on our Windows 2022 server: • Use Ansible to Manage Windows Servers...
Use Ansible to install Apache: • Use Ansible to Manage Windows Servers...
#######################
Windows server commands:
Below are the commands I ran in this turorial:
Get-WindowsCapability -Online | Where-Object Name -like 'OpenSSH*'
Add-WindowsCapability -Online -Name OpenSSH.Client~~~~0.0.1.0
**--------------
Add-WindowsCapability -Online -Name OpenSSH.Server~~~~0.0.1.0
Alternatively use this command to install:
dism /Online /Add-Capability /CapabilityName:OpenSSH.Server~~~~0.0.1.0
**------------
Start-Service sshd
Set-Service -Name sshd -StartupType 'Automatic'
if (!(Get-NetFirewallRule -Name "OpenSSH-Server-In-TCP" -ErrorAction SilentlyContinue | Select-Object Name, Enabled)) {
Write-Output "Firewall Rule 'OpenSSH-Server-In-TCP' does not exist, creating it..."
New-NetFirewallRule -Name 'OpenSSH-Server-In-TCP' -DisplayName 'OpenSSH Server (sshd)' -Enabled True -Direction Inbound -Protocol TCP -Action Allow -LocalPort 22
} else {
Write-Output "Firewall rule 'OpenSSH-Server-In-TCP' has been created and exists."
}
############################
Create the hosts.ini file:
[ec2-user@ip-172-31-16-55 windows]$ cat hosts.ini
[win]
IP_ADDRESS
[win:vars]
ansible_user=Administrator
ansible_password=
ansible_connection=ssh
ansible_shell_type=cmd
ansible_ssh_common_args=-o StrictHostKeyChecking=no -o UserKnownHostsFile=/dev/null
ansible_ssh_retries=3
ansible_become_method=runas
Run win_ping:
$ ansible win -m win_ping
Now Setup the Playbook:
---
hosts: win
gather_facts: no
tasks:
name: test powershell
win_shell: |
get-host
register: result_get_host
name: display result_get_host
debug:
var: result_get_host
Run the playbook:
$ ansible-playbook -i hosts.ini win_ssh.yml
Next Add the installation of Apache to your playbook:
name: add directory
win_file:
path: C:\ansible_examples
state: directory
name: Download the Apache installer
win_get_url:
url: https://archive.apache.org/dist/httpd...
dest: C:\ansible_examples\httpd-2.2.25-win32-x86-no_ssl.msi
force: true
name: Install MSI
win_package:
path: C:\ansible_examples\httpd-2.2.25-win32-x86-no_ssl.msi
state: present
Now run the playbook again and check Apache is installed
Thanks for watching. I hope this helps some of you to get this working!
A subscribe and a like are always appreciated.
#ansible #windows #ssh